In the rapidly evolving landscape of modern transportation, the advent of connected vehicle platforms has revolutionized the automotive industry, offering unprecedented levels of convenience, efficiency, and user experience. However, this technological leap forward has simultaneously opened a Pandora’s Box of digital security vulnerabilities, transforming the traditional automobile from a purely mechanical entity into a complex, rolling computer network. This comprehensive analysis delves deep into the multifaceted security risks inherent in contemporary vehicle platforms, exploring their origins, implications, and the sophisticated countermeasures required to safeguard our mobile digital ecosystems. The integration of telematics, infotainment systems, Advanced Driver-Assistance Systems (ADAS), and the inevitable progression toward fully autonomous vehicles have created a vast and attractive attack surface for malicious actors, making automotive cybersecurity not merely a technical concern but a critical issue of public safety and data privacy.
A. The Architectural Evolution and Its Inherent Vulnerabilities
The modern vehicle is no longer a standalone mechanical device; it is a sophisticated “platform on wheels.” This platform typically integrates over 100 Electronic Control Units (ECUs), millions of lines of code, and multiple communication buses (like CAN, LIN, FlexRay, and Ethernet). This complex architecture enables features ranging from engine management and brake control to navigation and streaming entertainment. The fundamental vulnerability lies in the historical design paradigm of these systems. For decades, automotive networks were developed under a “security by obscurity” model, relying on closed, proprietary systems assumed to be inaccessible. Connectivity has shattered this assumption.
The primary architectural weakness is the increasing interconnection between critical safety domains (like powertrain and braking) and non-critical informational domains (like infotainment and telematics). While gateways are employed to filter communication, researchers have repeatedly demonstrated that these barriers can be breached. An attack vector as seemingly innocuous as a compromised music streaming app or a malicious file on a connected smartphone can serve as a beachhead to pivot into safety-critical systems. This erosion of boundaries is the core challenge in vehicle platform security, creating scenarios where a hacker could potentially manipulate steering or braking through the vehicle’s Bluetooth or cellular connection.
B. Primary Attack Vectors and Methodologies
Understanding the pathways through which attackers can compromise a vehicle is essential for developing robust defenses. These vectors have grown in number and sophistication alongside vehicle connectivity.
B.1. Remote Exploitation via Cellular and Wi-Fi Interfaces
The built-in telematics control unit (TCU) provides always-on internet connectivity for services like emergency calling, remote diagnostics, and vehicle tracking. This cellular modem is a direct pipeline from the outside world into the vehicle’s core network. Security researchers have famously executed remote hacks by exploiting vulnerabilities in these cellular stacks, allowing them to send crafted packets that ultimately reach the CAN bus. Similarly, in-vehicle Wi-Fi hotspots, designed for passenger convenience, can be targeted if not properly segmented and secured with strong encryption and authentication protocols.
B.2. Short-Range Wireless Compromise (Bluetooth, Key Fobs, NFC)
Proximity-based attacks remain highly effective. Bluetooth interfaces for phone pairing and audio streaming have been found vulnerable to fuzzing and buffer overflow attacks. Furthermore, Passive Keyless Entry and Start (PKES) systems are susceptible to relay attacks, where thieves use signal amplifiers to extend the range of a key fob inside a home, tricking the car into unlocking and starting. Tire Pressure Monitoring Systems (TPMS), which wirelessly transmit data, can also be spoofed or jammed, providing false warnings or masking actual tire issues.
B.3. Physical Access Ports (OBD-II, USB)
The On-Board Diagnostics (OBD-II) port, mandated for emissions testing and repair, is a physically accessible goldmine for attackers. Plug-in devices (like insurance dongles or malicious tools) can provide unfiltered, direct access to the CAN bus. From here, an attacker can flash malicious firmware to ECUs, eavesdrop on traffic to reverse-engineer protocols, or inject commands. USB ports for media playback and charging are also risky; a maliciously crafted file on a USB drive could exploit vulnerabilities in the media parser or file system of the infotainment unit to gain a foothold.
B.4. Supply Chain and Backend Server Vulnerabilities
The attack surface extends far beyond the vehicle itself. Automotive manufacturers rely on complex supply chains for software and hardware components. A vulnerability in a third-party library used by a Tier-1 supplier can propagate to millions of vehicles. Moreover, the backend servers that manage vehicle fleets processing remote unlock commands, software updates, and user data are high-value targets. A breach of these servers could enable a mass, simultaneous attack on an entire model line or the theft of vast amounts of personal customer data.
B.5. V2X Communication Threats
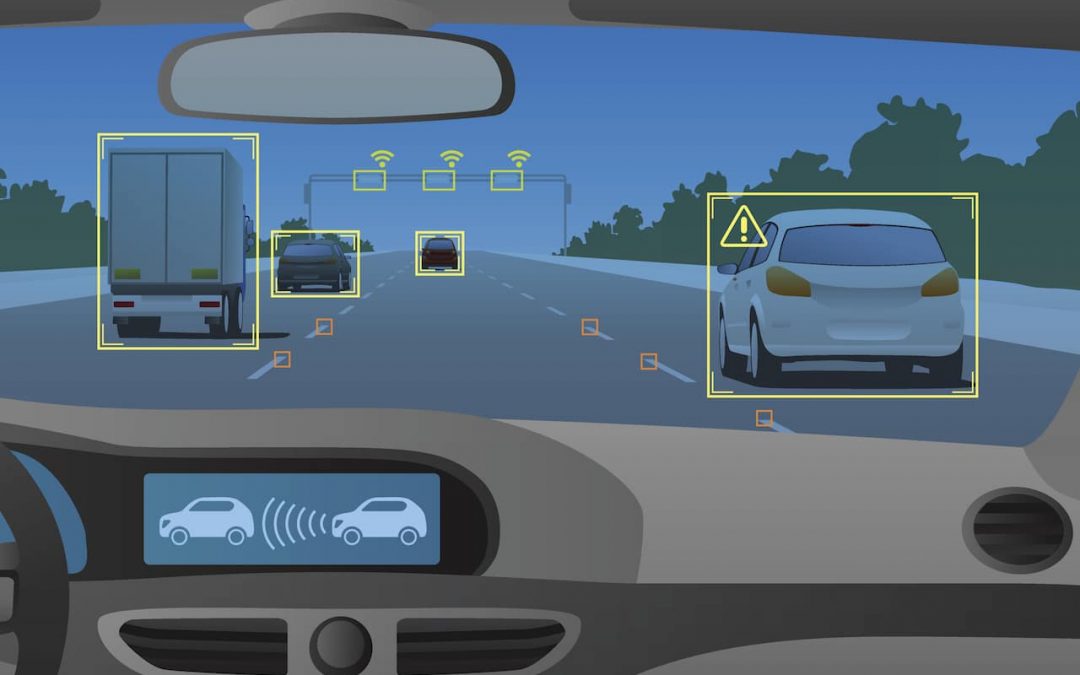
As Vehicle-to-Everything (V2X) communication rolls out, enabling cars to “talk” to each other (V2V), infrastructure (V2I), and pedestrians (V2P), it introduces a new frontier of risk. Spoofed V2X messages could create phantom vehicles on a dashboard display, trigger false emergency braking, or optimize traffic light patterns for a hacker’s convenience, causing widespread congestion. Ensuring the integrity and authenticity of these broadcasts is a monumental cryptographic challenge.
C. Consequences and Real-World Implications of a Breach
The potential fallout from a successful cyberattack on a vehicle platform is severe and multi-dimensional, extending beyond simple nuisance to matters of life and death, privacy, and economic stability.
C.1. Safety-Critical System Manipulation
The most terrifying scenario is the direct compromise of driving functions. Demonstrations have shown the ability to disable brakes, abruptly steer a vehicle, or kill the engine while in motion. In an era of drive-by-wire systems, where physical linkages are replaced with electronic signals, the integrity of these signals is paramount. An attack could also disable safety systems like airbags or electronic stability control during a crash, exponentially increasing the risk of fatal injury.
C.2. Privacy Invasions and Data Theft
Modern vehicles are prolific data collectors. They log GPS location history, driving habits (speed, braking patterns), biometric data (from seats or cameras), call logs, contact lists, and even microphone audio from hands-free systems. A compromised platform turns the car into a rolling surveillance device. This data is not only valuable for targeted advertising but could be used for stalking, corporate espionage, or blackmail. The aggregation of this data on manufacturer servers presents a lucrative target for ransomware attacks.
C.3. Financial Theft and Ransom
Cyber-physical theft is a growing trend. Hackers can clone digital keys or exploit relay attacks to steal vehicles outright. More subtly, they could enable “ransomware” attacks on a car, locking the owner out or disabling it until a cryptocurrency payment is made. Fleet-wide attacks could paralyze logistics companies, car rental services, or ride-sharing platforms, leading to massive financial losses and extortion opportunities.
C.4. Broad Systemic and Trust-Based Repercussions
A single, high-profile hack leading to fatalities could shatter public trust in connected and autonomous vehicles, derailing technological adoption for years. It could also lead to catastrophic liability for manufacturers and monumental regulatory fines under data protection laws like GDPR. On a larger scale, coordinated attacks could cause traffic chaos in major urban centers, creating a novel form of cyber-terrorism.
D. The Multilayered Defense Strategy: Building a Cyber-Resilient Vehicle
Mitigating these risks requires a holistic, defense-in-depth approach that spans the entire vehicle lifecycle, from initial design to decommissioning. Relying on a single security layer is a recipe for disaster.
D.1. Secure Hardware Foundations and Network Segmentation
Security must begin with hardware. ECUs should incorporate hardware security modules (HSMs) to securely store cryptographic keys and perform encryption/decryption operations. These HSMs are tamper-resistant, making key extraction extremely difficult. Crucially, the vehicle network must be rigorously segmented using next-generation, intelligent gateways that act as firewalls. These gatewalls must enforce strict, whitelisted communication policies between domains (e.g., blocking any CAN message from the infotainment cluster destined for the brake controller) and continuously monitor traffic for anomalies.
D.2. Robust Cryptographic Protocols and Secure Boot
Every communication channel, both internal and external, must be protected with state-of-the-art cryptography. This includes authenticated encryption for CAN bus messages (using standards like AUTOSAR SecOC), TLS for cellular/Wi-Fi data, and digital signatures for all software updates. A chain of trust must be established from the moment the vehicle powers on through a process called “secure boot.” Each ECU must cryptographically verify the integrity and authenticity of its software from the bootloader up to the application, preventing the execution of any tampered or unauthorized code.
D.3. Continuous Monitoring, Intrusion Detection, and Response
Given the persistent threat, vehicles need an immune system. An Automotive Intrusion Detection and Prevention System (AIDPS) should be deployed to analyze network traffic, ECU behavior, and diagnostic data in real-time. Using a combination of signature-based detection (known attack patterns) and anomaly-based detection (deviations from normal behavior), the AIDPS can identify a hack in progress. Upon detection, it must be capable of initiating containment actions such as isolating a compromised ECU, reverting to a safe mode, or alerting both the driver and a backend security operations center (SOC).
D.4. Secure Over-the-Air (OTA) Updates and Lifecycle Management
The ability to patch vulnerabilities is non-negotiable. Secure OTA update mechanisms are the single most important tool for maintaining vehicle security post-production. This process must be end-to-end secure: updates signed by the manufacturer, delivered via an encrypted channel, and validated by the vehicle’s HSM before installation. Manufacturers must also establish transparent vulnerability disclosure programs with security researchers and commit to providing security patches for the vehicle’s entire operational lifespan, which can exceed 15 years a stark contrast to the support cycle for consumer electronics.
D.5. Industry-Wide Collaboration and Standardization
No single manufacturer can solve this alone. The industry must move beyond proprietary solutions and embrace open, standardized frameworks. Initiatives like ISO/SAE 21434 (Road vehicles Cybersecurity engineering) provide a crucial process standard for building cybersecurity into vehicle development. Similarly, UN Regulation No. 155 mandates a certified cybersecurity management system for vehicle type approval in many markets. Sharing anonymized threat intelligence through organizations like AUTO-ISAC (Automotive Information Sharing and Analysis Center) is vital for the ecosystem to collectively prepare for and respond to emerging threats.
E. The Future Horizon: Quantum Computing and Autonomous Vehicles
The security challenge is a moving target. The impending arrival of quantum computing threatens to break current public-key encryption algorithms (like RSA and ECC) that underpin today’s digital certificates and key exchanges. The automotive industry must begin its “crypto-agility” journey now, preparing to migrate to quantum-resistant cryptographic algorithms. Furthermore, the progression to Level 4 and 5 autonomy will exponentially increase the vehicle’s dependence on external data from sensors, maps, and V2X. Ensuring the veracity of this sensory input protecting against adversarial machine learning attacks that fool object detection systems will be the next great frontier in automotive cybersecurity. The stakes will be even higher, as the vehicle’s operational safety will be entirely dependent on the integrity of its cyber-physical systems.
Conclusion: A Journey, Not a Destination

Securing the modern vehicle platform is one of the most complex engineering challenges of our time, sitting at the intersection of embedded systems, networking, cryptography, and artificial intelligence. It requires a fundamental cultural shift within the automotive industry, where security is treated with the same rigor as mechanical safety, baked into the design from the first line of code and the first circuit diagram. For consumers, awareness is key; understanding the connected features of a vehicle also means understanding the responsibility to keep its software updated. As we race toward an autonomous future, building a foundation of cyber-resilience is not optional it is the absolute prerequisite for earning and keeping the public’s trust. The security of our vehicles is, ultimately, the security of our lives, our privacy, and our mobility infrastructure. The work to fortify it must be relentless, collaborative, and innovative, ensuring that the road ahead is not only smart but also safe and secure.











